IS QL RIGHT FOR MY BUSINESS?
Stop chasing low-budget IT tickets
Let us bring you enterprise contracts. Partner with us to scale your MSSP or SaaS firm.
Recommended Channels

LinkedIn Ads are the primary weapon for reaching the C-Suite. Security decisions are high-stakes and committee-driven. We use Account-Based Marketing (ABM) to target CISOs, CIOs, and Compliance Officers at specific enterprise accounts, positioning your solution as the trusted choice for risk mitigation.

Google Ads captures immediate demand. When an IT Director searches for "Managed SOC Services" or "Ransomware Response," they have an urgent need. A robust strategy uses negative keywords to filter out students and "free antivirus" seekers, ensuring spend is focused purely on B2B buyers.

In security, trust is everything. Cyber Security Marketing Services must prioritize SEO to dominate search results for technical terms like "Zero Trust Architecture" or "HIPAA Compliance." Ranking for these informational queries builds the authority required to even be considered for an RFP.

Buyers are using AI to shortlist vendors. GEO/AEO ensures that when a prospect asks ChatGPT "Who are the top MSSPs for Financial Services?", your firm is recommended. We structure your technical content to be cited by these emerging search technologies.

The enterprise security sales cycle is long. Email Marketing is vital for both Nurture and Outbound. We build sequences that educate prospects on threat landscapes, compliance changes, and ROI, keeping your brand top-of-mind while the buying committee navigates internal approvals.

Security is abstract; threats are visceral. YouTube Ads allow you to visualize the impact of a breach or the ease of your remediation platform. Retargeting site visitors with educational video content significantly increases trust and accelerates the "know, like, trust" factor required for big deals.
SUPPORTING ELEMENTS
Security buyers are skeptical. We build dedicated landing pages for specific solutions (e.g., "Endpoint Protection" vs. "Cloud Governance"). These pages speak to the specific compliance needs (GDPR, SOC2) and technical requirements of the buyer, maximizing conversion rates.
In cyber, a lead is only valuable if they have budget. We feed pipeline data (Meetings Booked vs. Disqualified) back into the ad platforms. This trains the algorithms to find corporate buyers with real intent, rather than just IT students looking for whitepapers.
To capture Cyber Security interest early, strategies must offer utility. Assets like "Vulnerability Scanners," "Compliance Checkers," or "Risk Assessment Calculators" are highly effective. These tools provide immediate value to the user while capturing critical qualification data for your sales team.
We focus on Gross Profit and Pipeline Velocity. We report on "Cost Per Opportunity" and "Cost Per Deal," breaking down performance by channel. This ensures the marketing strategy is aligned with your business goals and is driving profitable growth, not just vanity metrics.
Speed to lead is critical. We work with our clients to set up CRM integrations (HubSpot, Salesforce) to ensure lead data flows instantly to your sales team. We help with this directly—you do not need to hire expensive external consultants to get your operations ready.
Attribution in long sales cycles is complex. We implement full-funnel tracking to understand how multiple touchpoints contribute to a closed deal. We rigorously test messaging and forms to improve conversion rates and lower your overall Customer Acquisition Cost (CAC).
IS QL RIGHT FOR MY BUSINESS?
COMMON QUESTIONS
20 – 80
2-6
OUR APPROACH
We choose for our team members to handle less clients, allowing them to immerse themselves in that business.
Ads Only
Ads, Landing Pages, Creative, Analytics and more
OUR APPROACH
We take responsibility for every element of a campaign. After all, the best ads in the world won’t work if you send them to the wrong place.
Traditional Agency
Marketing Jargon
Business English
OUR APPROACH
Our reporting is tailored to each client to ensure we’re focused on the metrics, objectives and tangible results that matter to them.
Cookie Cutter &
Set & Forget
Bespoke &
Constantly Iterating
OUR APPROACH
Campaign environments change daily. To keep up, we’re constantly iterating, seizing every opportunity, for daily enhancements.
Outsourced &
Delegated
to Juniors
Dedicated
Senior Marketer
OUR APPROACH
The person you speak with is the person developing and implementing your strategy, rather than a junior you’ve never met.
5-40%
0%
OUR APPROACH
A percentage of ad spend results in a misalignment of incentives. If we advise you to scale, it’s because it’s right for you.
Do You Want Better Results?
TESTIMONIALS
Improve Your Strategy

COMPLIMENTARY RESOURCE




COMPLIMENTARY RESOURCES
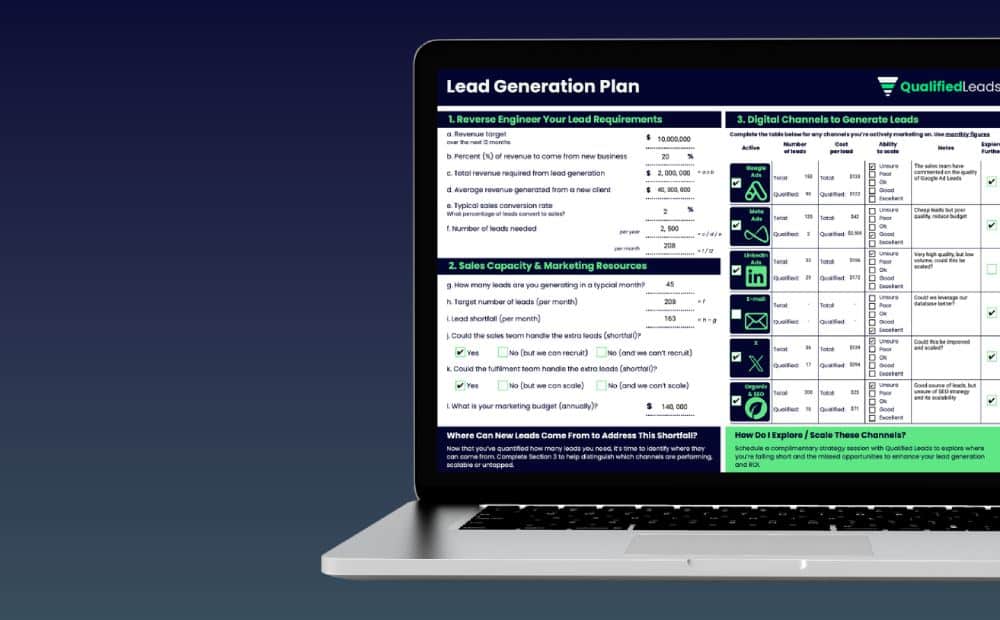




Find where to optimise your marketing, quantify ROI, reverse engineer acquisition costs, validate channels, and assess sales-marketing synergy.

Designed for business leaders to help you cut through the noise and understand whether you’re getting value from your digital marketing partner.
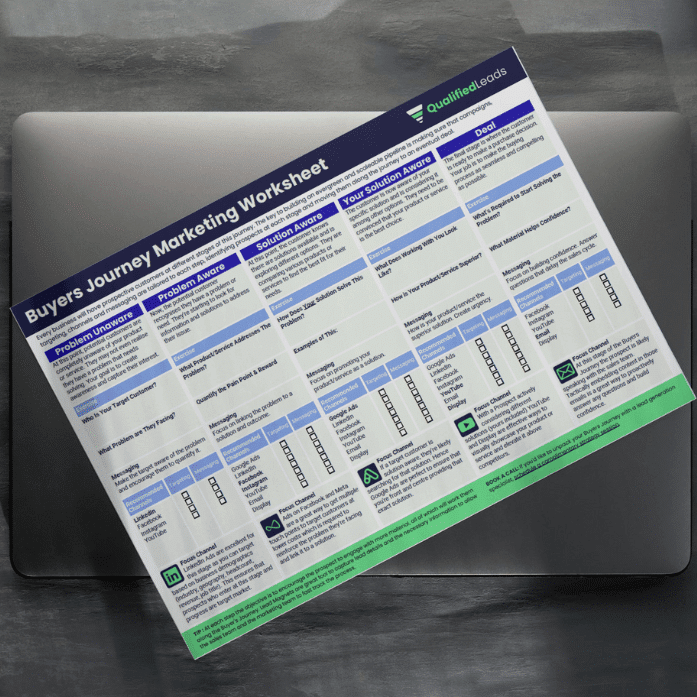
This worksheet will help you to achieve higher converting campaigns and generate more winnable sales conversations.
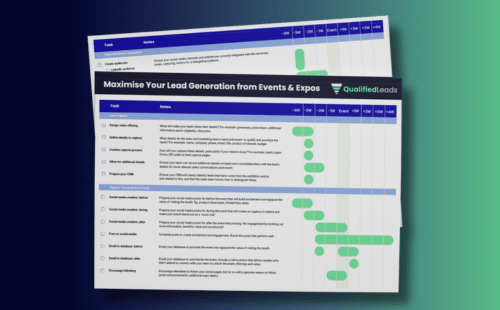
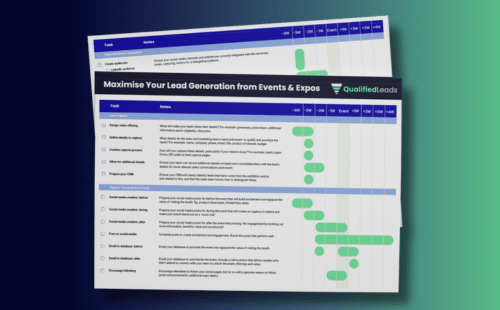
Events and expos are great opportunities to generate leads in person. Learn how you can amplify these efforts with digital marketing.
Waterflow
Aurora Financial
Coffee Culture
Younicorn
Crossvale
Aurora Financial
Ako Mātātupu
Projectus
If you’re serious about wanting to increase the quantity and quality of your leads, schedule a Free Strategy Call